OWASP Top 10 training for Burp Suite
Hello and welcome again in this OWASP Top 10 training series. In this blog post, you will setup Burp Suite. Then, you will configure it to capture HTTP traffic.
By the end of this blog post, you will have everything ready to start practicing all the OWASP Top ten vulnerabilities.If you would like to setup Zaproxy instead, I prepared a step-by-step guide to do it here. My suggestion is to setup both OWASP Zap and Burp Suite and get yourself comfortable in working with them. They are both the best tools to have under your ethical hacking belt.
OWASP Top 10 training setup steps for Burp Suite
Burp Suite is a web application security testing collection of tools developed by Portswigger Web Security. If this doesn’t ring a bell with you, you should add @albinowax in your Twitter account and google Postwigger Academy, you will thank me later 😉
Burp Suite is a great piece of software which enables you to perform the same tasks as OWASP Zap does. It comes with a free, Pro and enterprise version. The Pro version includes the Burp Scanner, which is for automated(ish) testing. The enterprise version is meant for enterprise environments where you need to constantly scan your assets.
For now, all you have to know is that the free version is more than enough for the purpose of this training.
Setup Burp Suite Community Edition
- As we did with Owasp Zap, go to the download page and download Burp Suite Community Edition. This is the free version.
- Follow the setup instructions by clicking the Next button.
- When the installation is done, click on the Finish button.
- When you open Burp Suite, you will have the only option to use a temporary project, which is fine for our case. Click Next. Then click “Start Burp”.
Configure Burp Proxy settings
- In the top left you can see tabs. Click on the one named “Proxy”, then the tab Options
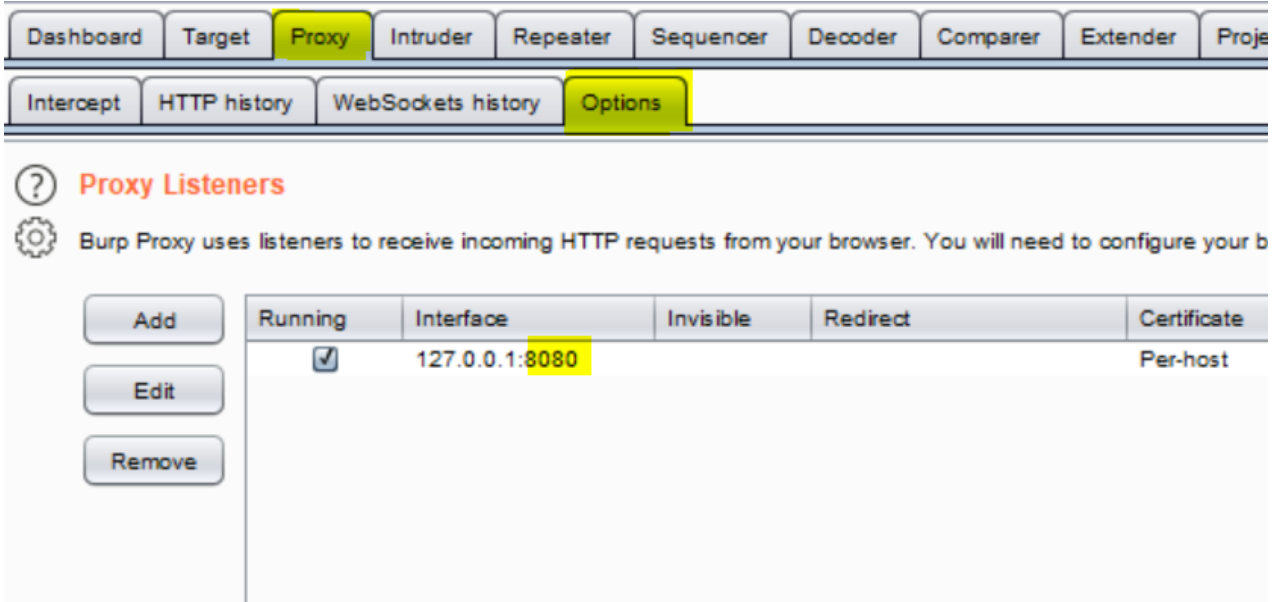
- Make sure you change the port to 8087, or any other port that you’d like which doesn’t interfere with an already running service. Remember that if you have Zaproxy running from the previous episode, you obviously cannot use its port in Burp Suite.
Configure the web browser
- To configure Foxyproxy add-on, follow the same steps as we have done in Zaproxy and create a new proxy with the port 8087. Give it a meaningful name, like “Burp”
- Now we are going to import Burp CA certificate. Go to http://burp, make sure that you have chosen Burp as your proxy in FoxyProxy.
- Click on CA Certificate on the top right corner of the web page.
- Follow the same steps as we did in the Zaproxy setup part to import the downloaded certificate into Firefox.
Testing HTTP traffic with Burp Suite
- Go to the Proxy tab, then the Intercept tab
- Disable “Intercept is on”, and click on the “HTTP history” tab
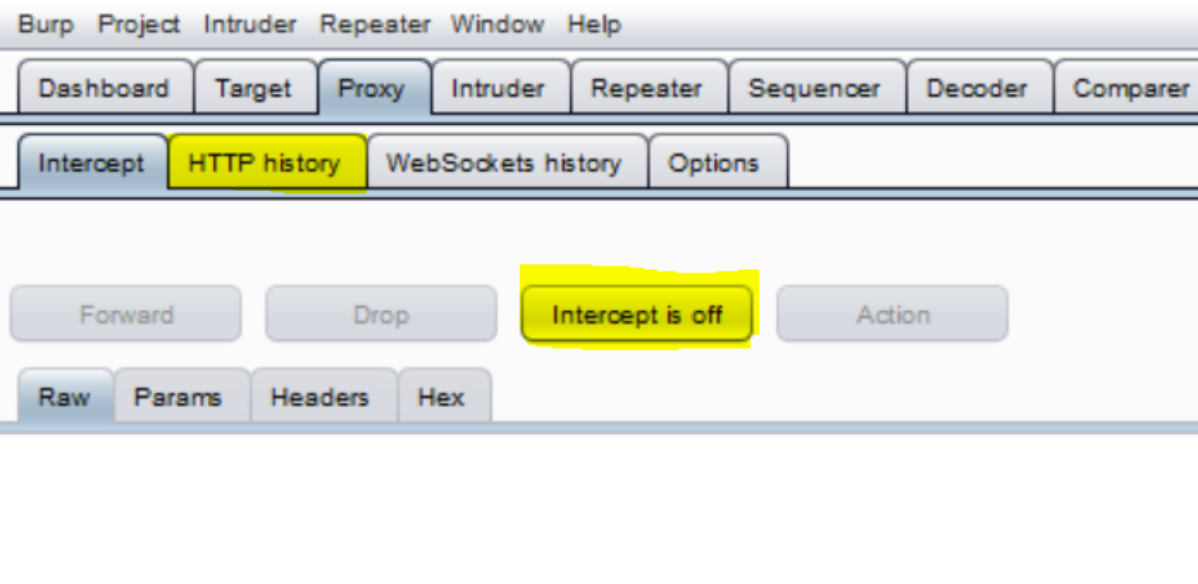
- Go to any web page on your Firefox browser, you should see HTTP traffic coming through Burp Suite in the HTTP history.
Congratulations! You’ve made another step forward towards practicing OWASP Top 10 vulnerabilities! In the next episodes, we will set up and configure our vulnerable web applications.
That’s it for today! I hope you enjoyed reading this blog post. Stay tuned for the next one. If you’d like to be notified when there is news on thehackerish.com, please subscribe to the Newsletter below. Until then, stay curious, crave for learning, be ethical and share with the world!
Find the video here