OWASP Top 10 training setup for OWASP Zap
Hello and welcome to this first blog post in the OWASP Top 10 training series where we will setup OWASP Zap to exploit OWASP Top ten vulnerabilities. Chances are that you are already familiar with OWASP Top 10 and are looking for ways to practice them. Let me tell you that you made a great decision, and I’m honored to help you continue your journey of learning. However, if you are not familiar with the theory behind OWASP Top 10 vulnerabilities, I highly suggest you learn them before.
OWASP Top 10 training summary
In this OWASP Top 10 training series, you will practice the exploitation of most OWASP Top 10 vulnerabilities both in Java and NodeJs. You will learn how to leverage the power of the best web proxies and you will understand why you were able to exploit the vulnerabilities. It is going to be a very exciting journey, so let’s get started!
In this blog post, you will setup your lab using the OWASP Zap. Then, you will configure them to capture HTTP traffic.
By the end of this blog post, you will have your favorite proxy ready for the next step.
Zaproxy setup for OWASP Top 10
Zap is the open-source web application security testing which belongs to OWASP, it is one of their flagship projects. It proxies HTTP traffic and allows to inspect, modify and resend them to test for security vulnerabilities. Zaproxy has many other features, like spidering web applications and performing automated scans, plus many more! It comes in many packages; you can even run it on your VPS on HTTP and have the same user interface as the Desktop one! For now, we are just going to use the bare minimum as the focus is the OWASP Top 10.
Download and install OWASP Zap
- You first need to download the Desktop version. Go to the Zaproxy Wiki page and download according to your OS.
- Then, install it as you normally would in your OS. I will be using a Windows box for the remaining steps. However, it should be straight forward for you as it is just a matter of clicking Next.
- Choose a Standard installation when prompted as shown below

- When you finish the installation, go ahead and open Zaproxy
- For now, we will not persist our Zap session, so just click start as you can see below

- Go to Tools and choose Options at the bottom
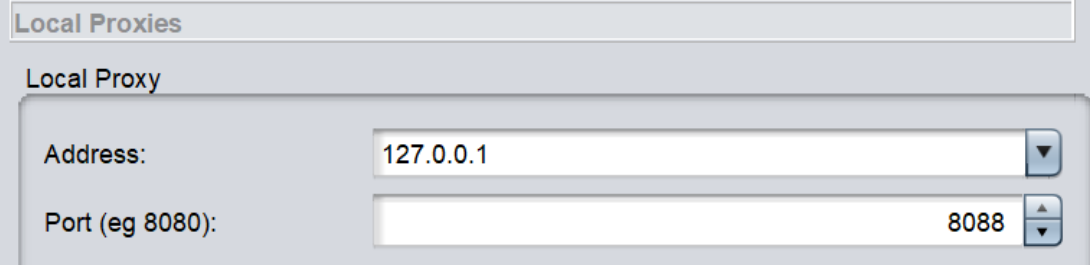
- In the menu on the left, click on Local Proxies
- Verify that your Address is set to 127.0.0.1 and that the Port is something other than 8080. I will be using 8088, so choose the same to avoid any troubles throughout this training.
Configure the web browser
For now, we will configure the Web Browser with OWASP Zap. I personally recommend using Firefox. In fact, I’ve had some issues setting up Chrome in the past; I wasn’t able to capture the traffic as expected from localhost. Anyways, feel free to use whatever you choose. In case things don’t work as intended, go back to this step and use Firefox.
- First, we will generate a Zaproxy Dynamic Certificate. This is optional, but will allow you to work with HTTPS web applications. So go to Tools > Options as you did before for the Zaproxy listener, and choose Dynamic SSL Certificates.
- Click Save as shown below

- Choose your destination file and save the Zaproxy root CA.
- On Firefox, type “about:preferences” in the address bar and search for Certificates, see the screenshot below

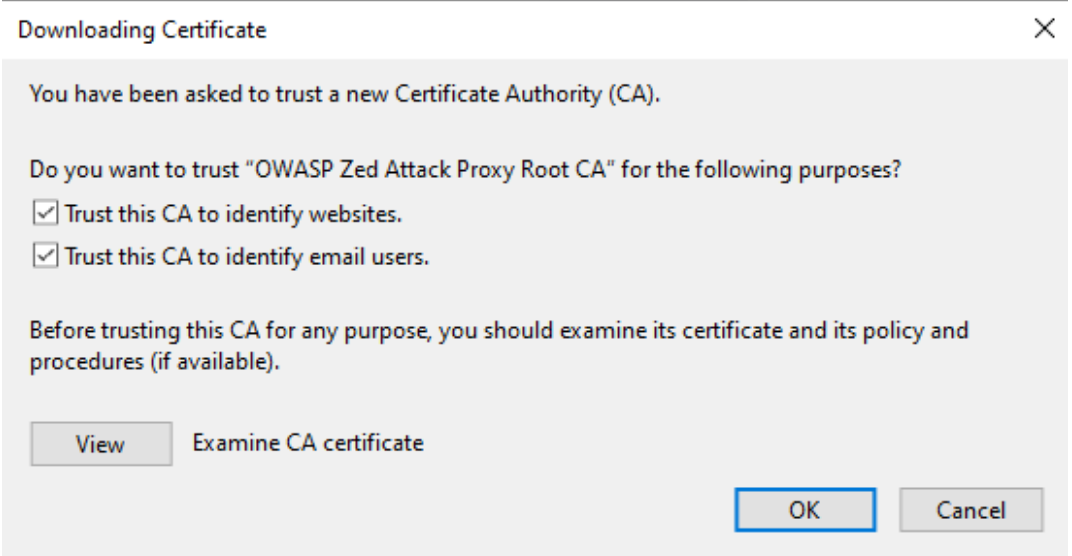
- Click on View Certificates. Under the Authorities tab, choose Import and locate your previously generated Zaproxy root CA file.
- Check both boxes as seen below and hit OK
Setting up Firefox proxy settings
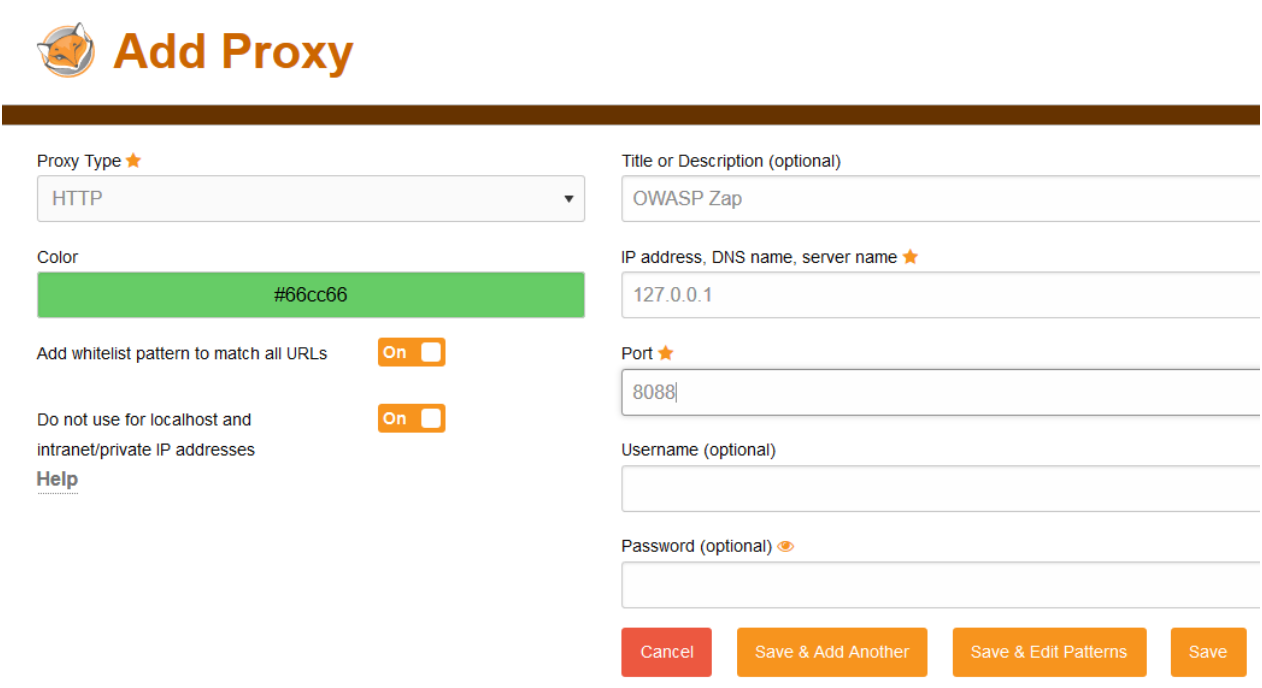
I’m going to use the well-known FoxyProxy add-on for that. It allows for more flexibility and makes it more reliable to capture HTTP traffic.
- On Firefox, go to this addon page and install it.
- You will have a new icon of a fox next to your Browser’s address bar.
- Click on it and choose Options in the drop-down menu.
- On the top left corner, click on Add. Make sure that your IP address is 127.0.0.1 and your Port is 8088 or whatever port number you set earlier. I named it “OWASP Zap”, feel free to name is however you like, then click on Save.
- Now, click on the fox icon next to your Firefox’s address bar and choose the newly created proxy.
- Make sure Zaproxy is up and running, then visit a webpage of your choice. You should see that you have some HTTP traffic going through Zaproxy.

Congratulations! You’ve made a step forward towards practicing OWASP Top 10 vulnerabilities!
For a penetration testing career, I find it good to be fluent in both OWASP Zap and Burp Suite. I personally work with the latter. However, during an assessment, I had to tamper with Web Sockets before Burp Suite implemented this feature. I knew Zaproxy supported it. So I used Zaproxy and I was able to find cool bugs using the resend feature inside of OWASP Zap. So be open to learning new tools, you don’t know when it will come handy!
For this reason, I will also show you how to setup Burp Suite to achieve the same thing in the next blog post.
That’s it for today! I hope you enjoyed reading this blog post. Stay tuned for the next one. Subscribe to the Newsletter below to be notified when there is news on thehackerish.com. Until then, stay curious, crave for learning, be ethical and share with the world!
If you enjoy learning on Youtube, I prepared the Owasp Top 10 training videos series just for you. Here is the setup video.